I’ve been responsible for maintaining a number of WordPress websites in my time, some larger than others. This one, for example, gets almost zero traffic, but I like to think that the hits I do get to this site are people looking for very specific answers that I’ve been able to provide. Today I’m going to try and add another helpful insight about WordPress optimization and troubleshooting with the hopes that it might help someone else in the future.
Continue reading “Fixing Intermittent Slowness and Timeouts on WordPress Sites”Author: Nick Leghorn
Implementing a security.txt File on the NY Times Website
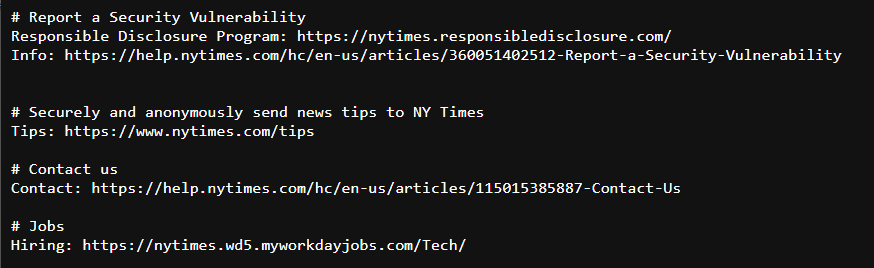
I finally did it — I achieved one of my lifelong goals: something I wrote was published on nytimes.com! Not exactly in the way you might imagine though, as the file that was published was a brand new security.txt file. You can read all about the concept and how it helps improve the security of The Times over at the Open blog, where the article I wrote was just published.
Configuring SNMP Monitoring for Fedora Workstation
I’m writing this more to remember this for myself than any other reason. I’ve had to do this a couple times, and every time I seem to forget the important steps. So here it is.
Continue reading “Configuring SNMP Monitoring for Fedora Workstation”LASCON 2021: Writing Policies That Aren’t Miserable for Everyone Involved

Policies. In theory they should be the backbone of any good information security program, but in reality few if any people actually read them and even fewer can understand what they mean. For ages we’ve been trying to solve this problem through education efforts, but maybe it’s time to look at how we construct policies in the first place and take a microservices approach to writing them?
You can download the full slide deck here:
Lead photo thanks to @SecurityBrew on Twitter!
Fixing AMP Ads That Break Your Website Layout
I maintain a couple of blogs, one of which is the whiskey review site Thirty One Whiskey. That blog actually gets a good amount of traffic, and generates enough revenue from Google ads to (partially) fund my whiskey and cigar habits.
One problem that I had been running into was that the default code for Google’s AMP ads was breaking the formatting of my website on mobile devices. When rendered, the ad element was wider than the width of the page on mobile screens, so when you started to scroll, quite often the page would move to the left a bit and the text would start to be cut off.
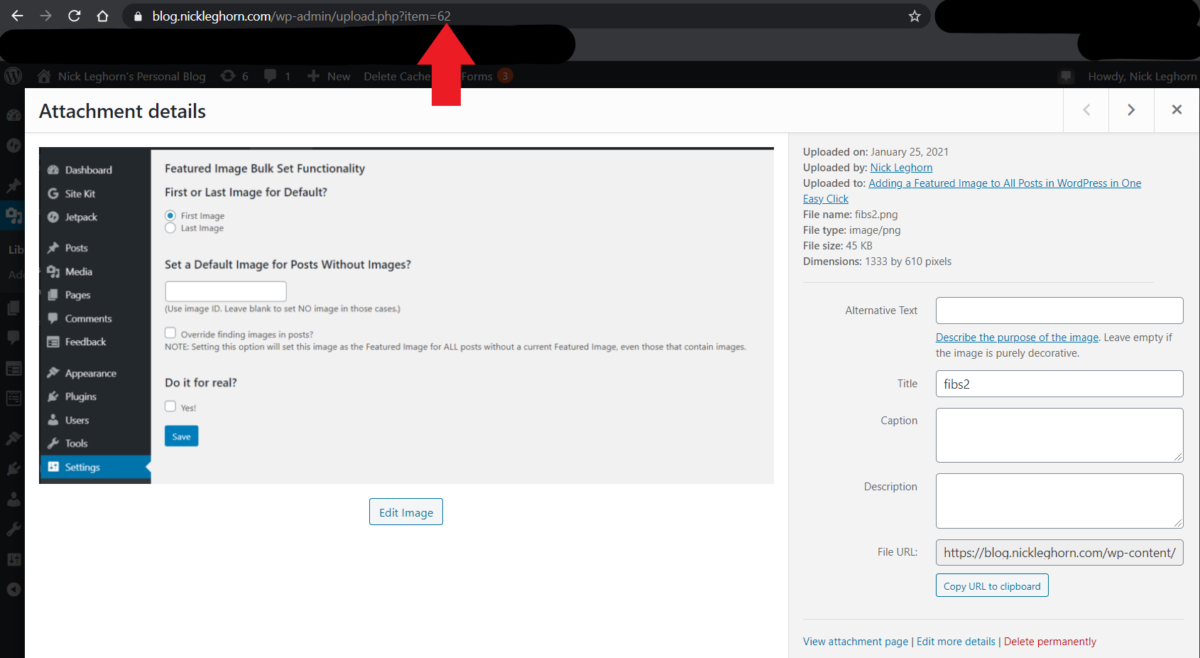
Continue reading “Fixing AMP Ads That Break Your Website Layout”Adding a Featured Image to All Posts in WordPress in One Easy Click
Featured images are sometimes an afterthought. For older bloggers, featured images weren’t really a critical part of the web layout and often weren’t added to posts. And for newer bloggers, it’s just one more step that doesn’t seem necessary. But then there comes a point where you want a new theme that requires featured images to work, and now you have hundreds of posts without that featured image.
Continue reading “Adding a Featured Image to All Posts in WordPress in One Easy Click”Querying And Displaying WordPress Site Stats Using a PHP Script
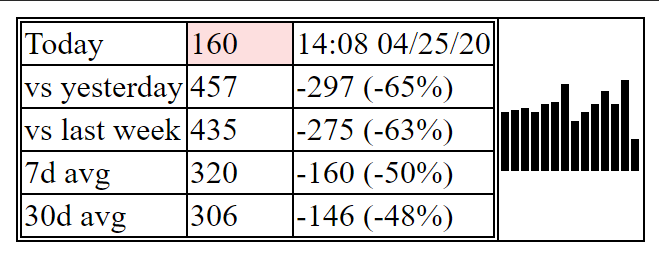
I like being able to keep an eye on everything that’s going on with the stuff I run. To that end I run a LibreNMS deployment in my house that monitors all my equipment, and I’v got a dashboard that gives me the vital statistics for everything I care about in one glance. One thing that has been sorely missing was a widget where I could see the stats for my WordPress sites, and I think I finally figured that out this week.
Continue reading “Querying And Displaying WordPress Site Stats Using a PHP Script”LASCON 2019: Learning the Power of the “Not My Responsibility” Mindset

This past week I was excited to present a talk on the work I’m doing at Indeed, specifically the implementation of a risk based information security management program and the benefits both to security engineers and the business.
Continue reading “LASCON 2019: Learning the Power of the “Not My Responsibility” Mindset”SpiceWorld Austin 2019: Docker for Dummies

This past week I presented my talk “Docker for Dummies” at the 2019 SpiceWorld Conference in Austin, Texas. If you’re looking for the slides then I’ve got good news! They’re posted right here.
For those looking for the direct GitHub link to the repository I mentioned with the scripts to set up your own LibreNMS docker environment then you can find it right here:
https://github.com/foghorn/librenmsdocker
The full video is available on YouTube here:
If you’re interested in having me present this talk to your company, group, or conference feel free to reach out through the contact methods listed at the end of the presentation.
SpiceWorld Austin 2019: Learning from Failure

This past week I presented my talk “Learning from Failure: Tales of Incident Response Gone Wrong” at the 2019 SpiceWorld Conference in Austin, Texas. If you’re looking for the slides then I’ve got good news! They’re posted right here.
The full video of the presentation is also available on YouTube here:
If you’re interested in having me present this talk to your company, group, or conference feel free to reach out through the contact methods listed at the end of the presentation.